What is Mobile Security?
Mobile security is a multi-layered defensive strategy designed to protect smartphones, tablets, and laptops from unauthorized access and data breaches. Unlike traditional PC security which relies on antivirus, mobile security is built on "Sandboxing" (isolating apps), "Hardware Attestation" (verifying device integrity), and "Encryption at Rest".
The 3 Pillars of Mobile Defense:
- 1. Device Security: Root of Trust and OS hardening.
- 2. Network Security: Encrypted tunnels and VPNs.
- 3. App Security: Containerization and Managed Play Stores.
Strategic Importance
For Private Enterprises
Focus is on "Intellectual Property (IP)" protection and "DLP (Data Loss Prevention)". In a BYOD (Bring Your Own Device) world, mobile security ensures that corporate data—like emails and CRM records—remains strictly separated from a user's personal apps, preventing accidental data leaks.
For Government Organizations
Requirements center on "National Security" and "Data Sovereignty". Government agencies often handle "Restricted" data that requires compliance with "MeitY/GoI" standards. They need hardware-backed attestation (like "Samsung Knox") to ensure that devices are not tampered with or rooted by state-sponsored actors.
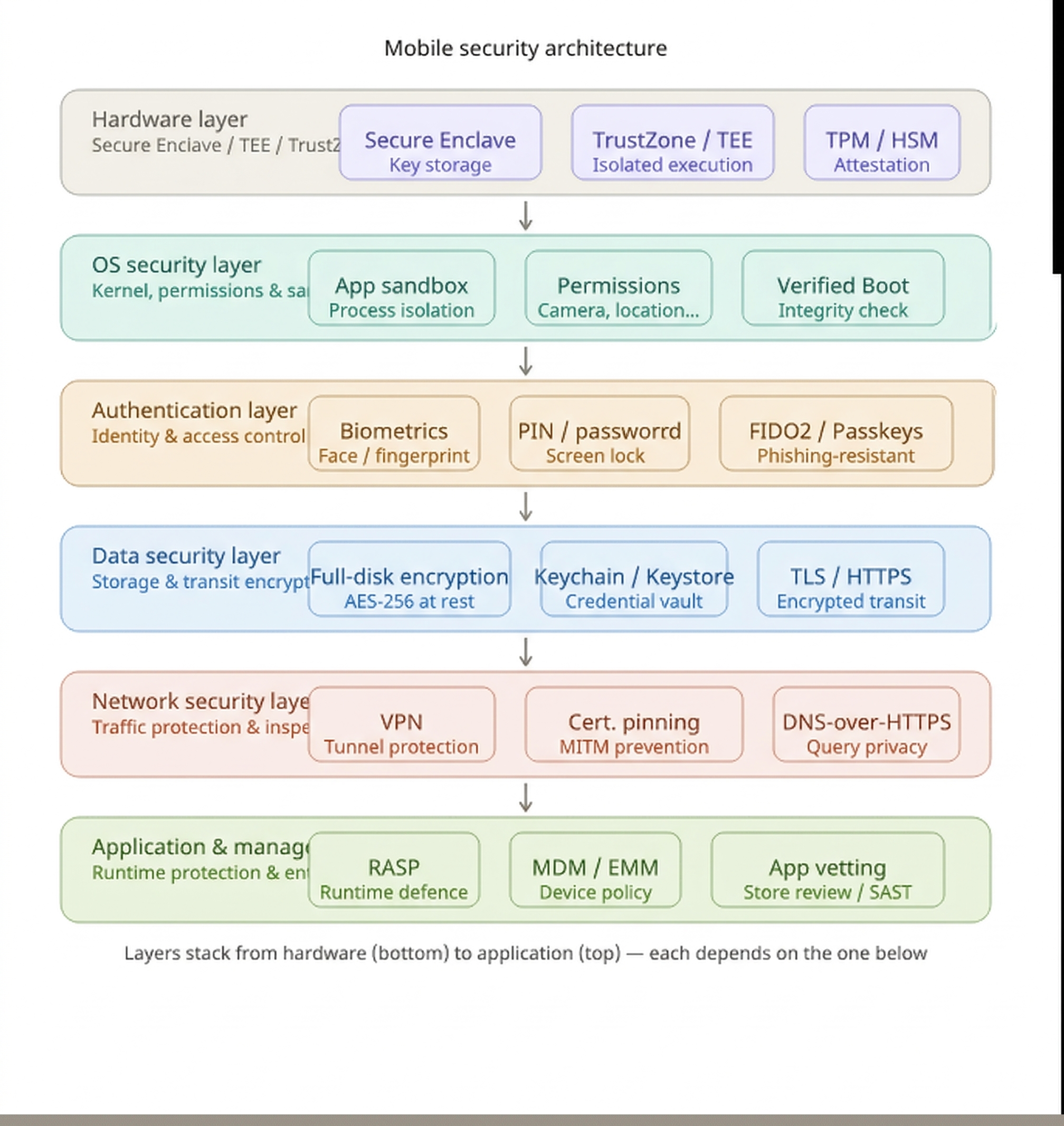
Mobile Security Architecture
While the theoretical stack is universal, its practical implementation differs.
Reference: Shivam Srivastava SeniorChief Portfolio Library.
Application & Management Layer
The top tier of the stack where RASP (Runtime Application Self-Protection) detects tampering at runtime. This layer handles MDM/EMM policy enforcement and rigorous app store vetting to catch vulnerabilities before deployment.
Network Security Layer
Protects traffic using VPNs and certificate pinning to prevent man-in-the-middle attacks, even if a rogue CA is present. DNS-over-HTTPS is implemented here to prevent query snooping.
Data Security Layer
Enforces AES-256 encryption for data at rest and TLS for data in transit. Platform keystores (iOS Keychain/Android Keystore) serve as secured vaults for all credentials and tokens.
Authentication Layer
Ties identity directly to the device hardware. Biometrics are processed inside the secure enclave so raw data never leaves the hardware, while FIDO2/Passkeys provide phishing-resistant authentication.
OS Security Layer
Builds on the hardware foundation with app sandboxing for process isolation, runtime permission grants, and Verified Boot to detect tampering during startup.
Hardware Layer (Root of Trust)
The ultimate foundation of trust. Technologies like Apple's Secure Enclave or Android's TrustZone/TEE physically isolate cryptographic keys and computations. TPMs and HSMs are utilized here for secure attestation.
Platform-Specific Security Architecture

Android Enterprise
The foundational framework provided by Google, utilizing a "hardened Linux kernel" and mandatory access controls (SELinux) to sandbox processes.
Verified Boot
Ensures system software integrity via cryptographic verification at every boot stage.
Work Profile
OS-level containerization that strictly separates personal data from corporate assets.
Samsung Knox
An advanced security layer rooted in the silicon, extending the Android baseline with hardware-backed integrity checks and real-time monitoring.
Knox Vault
Physically isolated hardware for storing high-value data like biometrics and root keys.
RKP (Real-time Protection)
Patented technology that monitors the Kernel for exploits every 50 milliseconds.
Apple iOS
A vertically integrated ecosystem where hardware and software co-evolve to provide strict boot-chain control and app lifecycle management.
Secure Enclave
Hardware-based key manager isolated from the main processor for crypto operations.
Managed Open-In
Policy framework restricting the flow of corporate data into unmanaged personal apps.
The Security Ecosystem
Category: UEM
The Policy Manager
Purpose: Centralized management of app deployment, device configuration, and compliance enforcement.
Key Players: Microsoft Intune, Knox Manage, SOTI.
Category: MTD
The Threat Hunter
Purpose: Real-time detection of network attacks (Wi-Fi), malicious apps, and OS vulnerabilities.
Key Players: Zimperium, Lookout, Pradeo.
Category: IAM
The Gatekeeper
Purpose: Verifies the identity of the user via MFA and FIDO2 before granting access to corporate data.
Key Players: Okta, Entra ID (Azure), Ping.