The Android Enterprise Paradigm
Android Enterprise is a holistic management and security framework designed to standardize how mobile devices are deployed in professional environments, ensuring consistency across a diverse hardware ecosystem.
A Legacy of Fragmentation
Initially, Android relied on the "Device Administrator" model. While useful, it lacked a standardized security framework, leading to inconsistencies across manufacturers and creating significant security gaps in multi-vendor fleets.
The Standardized Era
Today, Android Enterprise provides a unified set of APIs. This ensures that whether you are deploying a flagship smartphone or a rugged tablet, the core security and management capabilities remain consistent and robust.
2. The Multi-Layered Security Stack
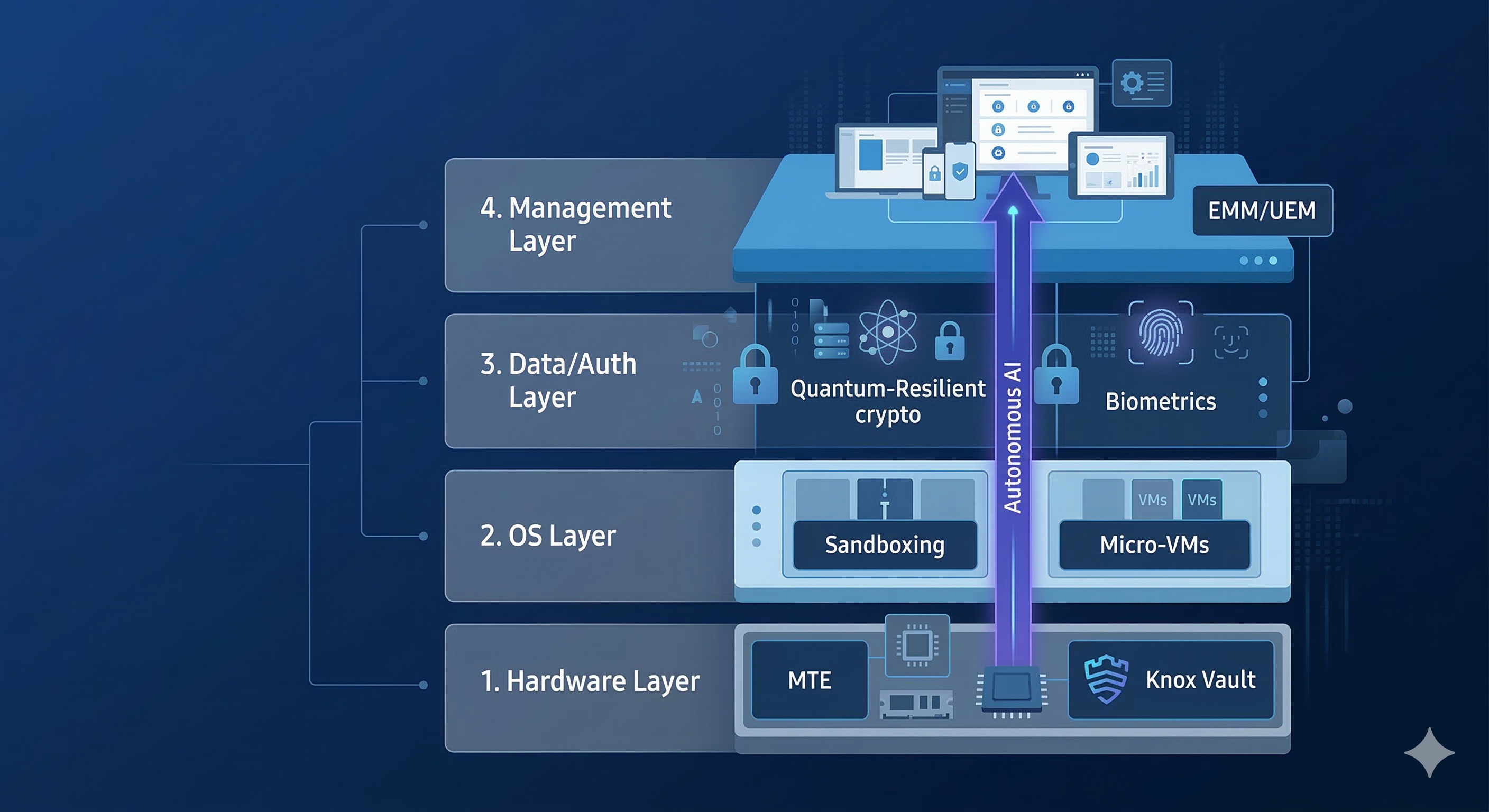
Hardware Root of Trust
The foundation of every security guarantee. Dedicated chips like Knox Vault or Titan M2 physically isolate biometric data and encryption keys from the main OS, making them inaccessible even if the kernel is compromised.
OS Sandboxing & Isolation
Utilizes Mandatory Access Control (MAC) via SELinux to ensure every app runs in a "sandbox." This isolation prevents malicious apps from reading data from your secure work containers.
Intelligence Layer
Google Play Protect scans over 100 billion apps daily using behavioral AI to detect zero-day threats before they can execute on your employees' devices.
3. Fleet Security via EMM/UEM
An Enterprise Mobility Management (EMM) solution acts as your centralized "Command Center," allowing you to orchestrate security across thousands of endpoints simultaneously[cite: 88, 90].
Policy Decision Point
The EMM constantly verifies device health. If a device fails compliance (e.g., skips an update), the EMM automatically revokes access to corporate email[cite: 126].
Managed App Ecosystem
Use the Managed Play Store to silently push approved apps and block unvetted software, ensuring your users only use secure tools[cite: 78, 163].
Selective Remote Wipe
Instantly remove work data from a lost or stolen device while leaving the user's personal photos and apps untouched—the perfect balance for BYOD[cite: 91, 109].
4. Strategic Management Modes
Work Profile (BYOD)
A visual briefcase separates work and life. IT manages the container; the user manages the phone. Ultimate privacy for employee-owned hardware.
Fully Managed (COBO)
The standard for company-issued hardware. Provides total transparency and control over every device setting and application install.
Dedicated Device (COSU)
Optimized for single-use scenarios like retail kiosks or delivery logistics. Locked to specific productivity apps.
5. The Future: Y26 Innovations
Memory Tagging Extension (MTE)
MTE is a hardware-level feature that "tags" memory allocations to detect and block memory-safety vulnerabilities. It is designed to neutralize nearly 70% of traditional memory exploits like buffer overflows before they can execute.
Quantum-Resilient Keystore
To counter the future threat of quantum computing, the 2026 stack introduces Post-Quantum Cryptography (PQC). This ensures your encrypted data remains secure against future decryption attempts.
6. Your Strategic Roadmap
Build a secure fleet in five professional stages.